You are gaining access to a system that you are not supposed to have access to is considered hacking. For example, login into an email account that is not supposed to have access, gaining access to a remote computer you are not supposed to access. Reading information that you are not supposed to read is considered hacking. There are a large number of ways to hack a system.
In 1960, the first known event of hacking had taken place at MIT, and at the same time, the term Hacker was organized.
Ethical hacking
Ethical hacking is also known as White hat Hacking or Penetration Testing. Ethical hacking involves an authorized attempt to gain unauthorized access to a computer system or data. Ethical hacking is used to improve the systems and networks’ security by fixing the vulnerability found while testing.
Ethical hackers improve the security posture of an organization. Ethical hackers use the same tools, tricks, and techniques that malicious hackers use, but with the authorized person’s permission. The purpose of ethical hacking is to improve security and defend the systems from malicious users’ attacks.
Types of Hacking
We can define hacking into different categories, based on what is being hacked. These are as follows:
- Network Hacking
- Website Hacking
- Computer Hacking
- Password Hacking
- Email Hacking
- Network Hacking: Network hacking means gathering information about a network to harm the network system and hamper its operations using various tools like Telnet, NS lookup, Ping, Tracert, etc.
- Website hacking: Website hacking means taking unauthorized access over a web server, database, and change in the information.
- Computer hacking: Computer hacking means unauthorized access to the Computer and steals the information from PC like Computer ID and password by applying hacking methods.
Password hacking: Password hacking is the process of recovering secret passwords from data that has already been stored in the computer system. - Email hacking: Email hacking means unauthorized access on an Email account and using it without the owner’s permission.
Advantages of Hacking
There are various advantages of hacking:
- It is used to recover the lost of information, especially when you lost your password.
- It is used to perform penetration testing to increase the security of the Computer and network.
- It is used to test how good security is on your network.
Disadvantages of Hacking
There are various disadvantages of hacking:
- It can harm the privacy of someone.
- Hacking is illegal.
- Criminals can use hacking to their advantage.
- Hampering system operations.
Type Of Hackers
Hackers can be classified into three different categories:
- Black Hat Hacker
- White Hat Hacker
- Grey Hat Hacker
Black Hat Hacker
Black-hat hackers are also known as an Unethical Hacker or a Security Cracker. These people hack the system illegally to steal money or to achieve their own illegal goals. They find banks or other companies with weak security and steal money or credit card information. They can also modify or destroy the data as well. Black hat hacking is illegal.
White Hat Hacker
White hat hackers are also known as Ethical Hackers or Penetration Tester. White hat hackers are the good guys of the hacker world.
These people use the same technique used by black hat hackers. They also hack the system, but they can only hack the system that they have permission to hack to test the system’s security. They focus on safety and protecting the IT system. White hat hacking is legal.
Gray Hat Hacker
Gray hat Hackers are a Hybrid between Black hat Hackers and White hat hackers. They can hack any system even if they don’t have permission to test the system’s security, but they will never steal money or damage the system.
In most cases, they tell the administrator of that system. But they are also illegal because they test the system’s security that they do not have permission to test. Grey hat hacking is sometimes acted legally and sometimes not.
Famous Hackers
In this section, we will see some of the famous hackers and how they become famous.
Jonathan James
Jonathan James was an American hacker. He is the first Juvenile who send to prison for cybercrime in the United States. He committed suicide on 18 May 2008, of a self-inflicted gunshot wound.
In 1999, at the age of 16, he gained access to several computers by breaking the password of a NASA server and stole the International Space Station’s source code, including control of the temperature and humidity within the living space.
Kevin Mitnick
He is a computer security consultant, author, and Hacker. He infiltrates his client’s companies to expose their security strengths, weaknesses, and potential loopholes. In the history of the united state, he was formerly the most wanted computer criminal.
From the 1970s up until his last arrest in 1995, he skillfully bypassed corporate security safeguards. He found his way into some of the most well-guarded systems like Sun Microsystems, Nokia, Motorola, Netcom, Digital Equipment Corporation.
Mark Abene
Mark Abene is an American Infosec expert and Entrepreneur. He is known around the world by his pseudonym Phiber Optik. Once, he was a member of the hacker groups Legion of Doom and Master of Deception. He was a high profile hacker in the 1980s and early 1990s.
He openly debated and defended the positive merits of ethical hacking as a beneficial tool for the industry. He is also an expert in penetration studies, security policy review and generation, on-site security assessments, systems administration, and network management, among many others.
Robert Morris
Robert Morris was the creator of the Morris Worm. He was the first computer worm to be unleashed on the Internet. The Morris Worm could slow down computers and make them no longer usable. Due to this, he was sentenced to three years probation, 400 hours of community service, and had to pay a penalty amount of $10,500.
Gary McKinnon
Gary McKinnon is a Scottish systems administrator and Hacker. In 2002, he was accused of the “biggest military computer hack of all time.” He has successfully hacked the network of Navy, Army, Air Force, NASA system of the United States Government.
In his statement to the media, he has often mentioned that his motivation was to find evidence of UFOs and the suppression of “free energy” that could potentially be useful to the public.
Linus Torvalds
Linus Torvalds is a Finnish-American software engineer and one of the best hackers of all time. He is the developer of the overall Unix-based operating system called Linux. Linux operating system is open source, and thousands of developers have contributed to its kernel. However, he remains the ultimate authority on what new code is incorporated into the standard Linux kernel.
Torvalds aspire to be simple and have fun by making the world’s best operating system. Linus Torvalds has received honorary doctorates from the University of Helsinki and Stockholm University.
Kevin Poulsen
Kevin Poulsen is an American former Black-hat hacker. He is also known as Dark Dante. He took over all the telephone lines of radio station KIIS-FM of Los Angeles, guaranteeing that he would be the 102nd caller and win a Porsche 944 S2.
Poulsen also drew the ire of the FBI, when he hacked into federal computers for wiretap information. As a result of this, he was sentenced for five years. He has reinvented himself as a journalist.
Ethical Hacking-Environmental Setup
To perform ethical hacking, we have to download the Kali Linux Operating System, and we can download Kali Linux OS inside the Virtual box. Here are the basic steps to download the virtual box and Kali Linux.
Step 1: Download Virtual Box
In step1, we download the Virtual box because the virtual box allows us to create a virtual machine inside our current operating system. After this, we will download the Kali Linux. A virtual machine is just like a completely separate working machine. You will lose nothing if you install an operating system inside the virtual machine. The operating system will perform just like the install on a separate laptop.

Now using the following link, you can download the virtual box according to your operating system and install it.
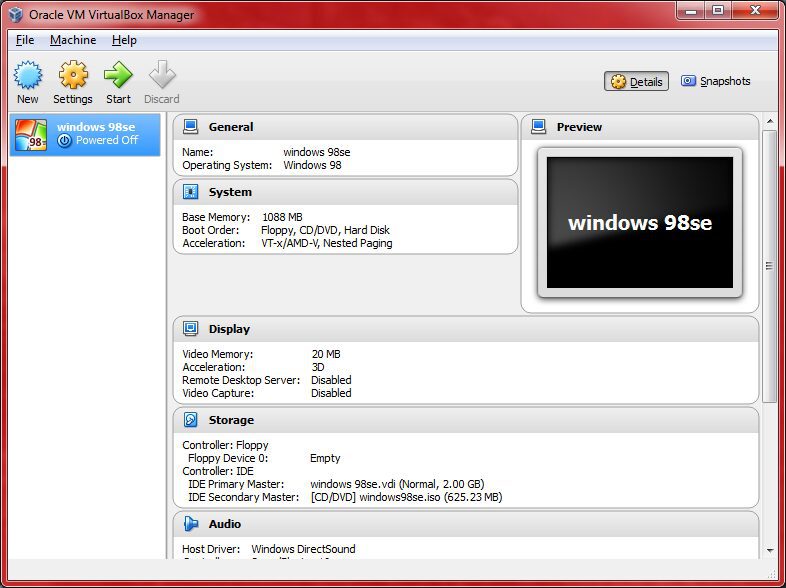
After installation, the virtual box will be shown as follows:
Step 2: Download Kali Linux
Now we will download the Kali Linux. It contained all the programs and application that we need to use pre-installed and preconfigured, that means we just need to install this operating system and start hacking.
There are two ways to install Kali. You can install it as a virtual machine inside your current operating system, or you can download it as a main operating system. In this tutorial, I am going to use a virtual machine.
Use the following link to download the Kali Linux operating system.
Now click on Kali Linux VirtualBox Images and download the Kali Linux according to the compatibility of your Operating System.
- Download the 64-bit version if your computer is 64 bits; otherwise, download the 32-bit version.
- The downloaded file has a .ova extension. If the file doesn’t have a .ova extension, that means you downloaded the wrong file.
After downloading, you will get a file with the .ova extension. Now, to install the Kali Linux, you need to just double click on the file and click on the import button.
After installation, the Kali Linux is ready to use and will look like as follows:
Step 3: Modify some settings of Kali Linux
Before starting, we will modify some Settings. So just click on Kali Linux on the left side and then click on the Settings.
Now click on system and modify the amount of RAM depending on the amount of RAM on your computer. You can give it as 2GB if you want, but 1GB is enough for Kali.
If you click on the Processor, then you can modify the amount of Processor as 2CPU, but 1 CPU is enough for Kali.
Now click on Network Settings and set “Attached to” as “NAT Network,” but sometimes the network is automatically created by the virtual box, and sometimes the virtual box doesn’t create this network automatically. If it is automatically created, then click OK. If it is not created, then the following screen will be shown:
If the virtual box is not automatically created the network, then just go to the VirtualBox → Preferences → Network → + sign. Now you can see that it creates another network.
Step 4: Starting of Kali Linux
Now we are starting the Kali Linux by clicking the start button. After clicking, two cases will arise:
- Sometimes it will run successfully.
- Sometimes you will get an error like this:
To fix this error, you have to download the Oracle VM VirtualBox Extension Pack of the same version of VirtualBox. To find the version of Virtual Box, just click on Help then click on About VirtualBox.
Now download the VirtualBox Extension of 5.2.20 version. Use the following link to download it:
Now click on Oracle_VM_VirtualBox_Extension_Pack-5.0.20.vbox-extpack and download it.
Install the VirtualBox extension pack. After installing, to check it clicks on File → Preferences → Extensions. Here you can see the Oracle VM VirtualBox Extension Pack. Click OK.
Now the problem is fixed, and we can start the virtual machine by clicking the start button.
After starting, it will ask us for the Username, and the default Username is root then it will ask us for the password and the default password is the reverse of root which is toor. Now you will get a screen like this:
Ethical Hacking-Network Penetration Testing
Network penetration testing is the first penetration testing that we are going to cover in this section. Most of the systems and computers are connected to a network. If a device is connected to the internet, that means the device is connected to the network because the internet is a vast network. Therefore, we need to know how devices interact with each other in a system, as well as how networks work.

Network penetration testing is divided into three subsections:
- Pre-connection attacks: In this section, we will learn about all the attacks that we can do before connecting to a network.
- Gaining attacks: In this section, we will learn how to crack Wi-Fi keys and gain access to the Wi-Fi network, whether they use WEP/WPA/WPA2 network.
- Post-connection attacks: These attacks apply whenever you can connect to the network. In this section, you will learn the number of powerful spells that will allow you to intercept the connections and capture everything like the user-name, password, URL, chat messages. You can also modify the data as it has been sent in the air. These attacks can apply to both Wi-Fi or wired networks.
Ethical Hacking-Basics Of Network
A network is a group of two or more devices that are connected to share the data or share the resource. A network contains many different computer systems that are secured by a physical or wireless connection like a server or router. This router has direct access to the internet. The device can only connect to the internet through the router or access point.
For example: Suppose the client or device connected to the network through Wi-Fi or Ethernet. If the client opens the browser and types google.com, then your computer will send a request to the router for asking google.com. The router will go to the internet and right google.com. The router will receive google.com and forward that response to the computer. Now the client can see google.com on the browser as a result.
In networking, devices on the same network communicate with each other using packets. If you send a video, log in a website, sending chat messages, sending an email, all the data is sent as packets. In networking, devices ensure that these packets go in the right direction using the mac address. Each box has the source mac and destination mac, and it flows from the source mac to destination mac.
Ethical Hacking-Pre-connection attack
The pre-connection attack is the first part of network penetration testing. To perform this attack, we will look at the fundamentals like how to show all the networks around us, how to find the details of all the connected devices to a particular system. Once we know about the structure and connected devices to it, we can disconnect any device without knowing the password of that device.
Following are the necessary steps we will be going through to perform Pre-connection attack:
- Wireless Interface in Monitor mode: In this step, we will change the way of the wireless device as Monitor mode.
- About airodump-ng: In this step, we will use airodump-ng to list all the network around us and display useful information about them.
- Run airodump-ng: In this step, we will see all the devices that are connected to a particular network and collect more information about it.
- Deauthenticate the Wireless client: In this step, we can disconnect any device which is shown in the previous step using the aireplay-ng.
Also Read:

